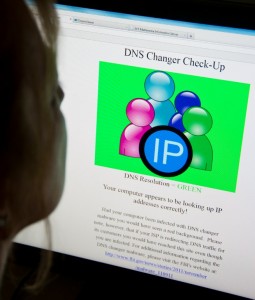
A woman looks at a website designed to check for problems stemming from malware known as DNS Changer, July 9, 2012, in Washington, DC. Tens of thousands of computer users around the world infected with malware last year may lose their Internet access Monday with the expiration of a fix by US authorities, security experts say. The so-called Internet doomsday virus, however, appeared to pose no major problems Monday in the first hours after a fix expired. AFP PHOTO/KAREN BLEIER
WASHINGTON—The so-called Internet doomsday virus with the potential to black out tens of thousands of computers worldwide appeared to pose no major problems Monday in the first hours after a fix expired.
Security firms reported no significant outages linked to the DNS Changer virus, as many Internet service providers have either implemented a fix or contacted customers with steps to clean their computers.
The problem stems from malware known as DNS Changer, which was created by a cybercriminals to redirect Internet traffic by hijacking the domain name systems (DNS) of Web browsers.
The ring behind the DNS Changer was shut down last year by the US Federal Bureau of Investigation (FBI), Estonian police and other law enforcement agencies, after infecting some four million computers worldwide.
Nearly 300,000 computers appeared to be still infected as of June, according to experts monitoring the problem.
On Monday, temporary servers set up by the FBI to direct Internet traffic normally, even for infected computers, were shut down.
But security specialists said most Internet users and providers have had time to work around or fix the problem.
“Many global operators are keeping their DNS Changer victims online, even after FBI stopped. We do not expect much noise about this today,” said Mikko Hypponen, chief research officer at the Finland-based firm F-Secure, in a Twitter message.
Johannes Ullrich of the SANS Security Institute said that for computers running Windows, the computer “may actually revert to the default settings once the DNS server is turned off.”
He added, that “if you used the bad DNS server, chances are that various entities tried to notify you. Google for example should have shown you a banner.”
Additionally, Ullrich said the malware is “old enough where antivirus, if you run any, should have signatures for it.”
Six Estonians and a Russian were charged in Estonia in November with infecting computers, including NASA machines, with the malware as part of an online advertising scam that reaped at least $14 million.
Because the virus controlled so much Internet traffic, authorities obtained a court order to allow the FBI to operate replacement servers until July 9.
The FBI, as well as Facebook, Google, Internet service providers and security firms have been scrambling to warn users about the problem and direct them to fixes.
A DNS Changer Working Group has been monitoring and educating people about the malware, with a website https://www.dcwg.org.
Experts said that if a computer is infected, they could still access the Internet by reconfiguring the way they access the domain name system.
Instead of entering an address such as ebay.com, they could use the underlying address, which is a series of numbers, said Marco Preuss of the Russian security firm Kaspersky on the company’s Securelist blog.
“If you know the address of the server you can still use it instead of the name, e.g. 195.122.169.23 is ‘securelist.com’ but this is not easy solution,” he said.
Others with more technical savvy can also reprogram their computer’s network settings, to access public DNS servers such as one operated by Google.
“If you are infected, you can change your DNS entries to the free DNS-Servers from Google: 8.8.8.8 and 8.8.4.4,” said Preuss.
“OpenDNS also offers two: 208.67.222.222 and 208.67.220.220, which we also recommend for additional security features.”