Massive cyber-espionage linked to China
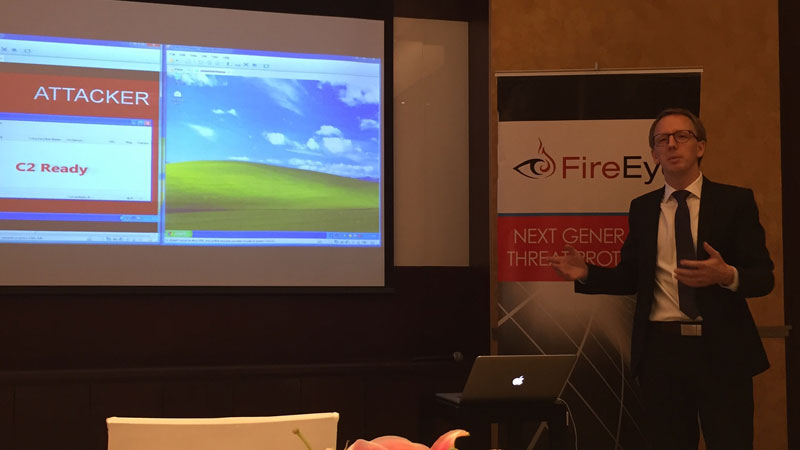
FireEye Inc. demonstrates how a cyber-attacker steals information from a victim using a virtualized computer system. Anthony Q. Esguerra, Inquirer.net
MANILA, Philippines—China may be behind a massive cyber-espionage on the computer systems of governments, military units, financial and media institutions as well as individual journalists across Southeast Asia.
In a report presented in Manila on Tuesday, Cybersecurity group FireEye Inc. said years of research and monitoring led to the discovery of a decade-long cyber-espionage campaign linked to China.
A threat group called APT 30, an advanced persistent threat group, has been consistently targeting Southeast Asian countries including Malaysia, Vietnam, Thailand and even India, South Korea, Saudi Arabia and the US. FireEye said the Philippines was a likely target.
“Advanced threat groups like APT 30 illustrate that state-sponsored cyber-espionage affects a variety of government and organizations in the Philippines and Southeast Asia,” Wias Issa, senior director at FireEye, said.
The massive group’s goal appeared to be “sensitive information theft for government espionage,” he added.
‘Well-funded, state sponsored’
Years of monitoring and analysis led FireEye to link the organized cyber-attacks to China.
APT 30 targets entities that may “satisfy governmental intelligence collection requirements” for political gain by the sponsor state, most likely China, the report suggests.
“What we realized was this is not a single person. This is not a handful of people. This is well-funded, likely state-sponsored with a coherent development plan that’s able to execute its mission successfully for at least a decade,” Issa said.
The firm said that analysis and back-engineering revealed that APT 30’s tools were programmed and developed in China.
“Our investigation also yielded that a Chinese-language keyboard was used to compile the data. Looking at that information, the toolsets–that’s one, the victimology, the people that they targeted and also the information that they’re after suggest that this is a Chinese-backed attack group that’s based in China that’s likely supporting the government of China,” Issa explained.
Severe attacks during regional events
On occasions convening the leaders of the region, FireEye has noticed severe and heightened attacks on China’s neighboring countries.
A lot of attacks happened during important decision-making events, such as the Association of Southeast Asian Nations summit, in the region.
“They have timed it specifically with Asean summit, multiple specific events. The compile times were right before or during the events and that’s going back to with some of debates in Asean 2013’s resolution on South China Sea,” said FireEye’s Patrick Neighorn.
The 2013 Asean summit in Brunei concentrated on the territorial disputes around South China Sea. At the summit, the Philippines made a strong call to address the issue at the regional level.
The Philippines, along with other countries claiming parts of the territory, made strong resistance against China’s expansionism in the disputed waters.
In the recent Asean summit, the Philippine government called on fellow Asean members to stand against China’s “bullying” and expansionism.
For comprehensive coverage, in-depth analysis, visit our special page for West Philippine Sea updates. Stay informed with articles, videos, and expert opinions.